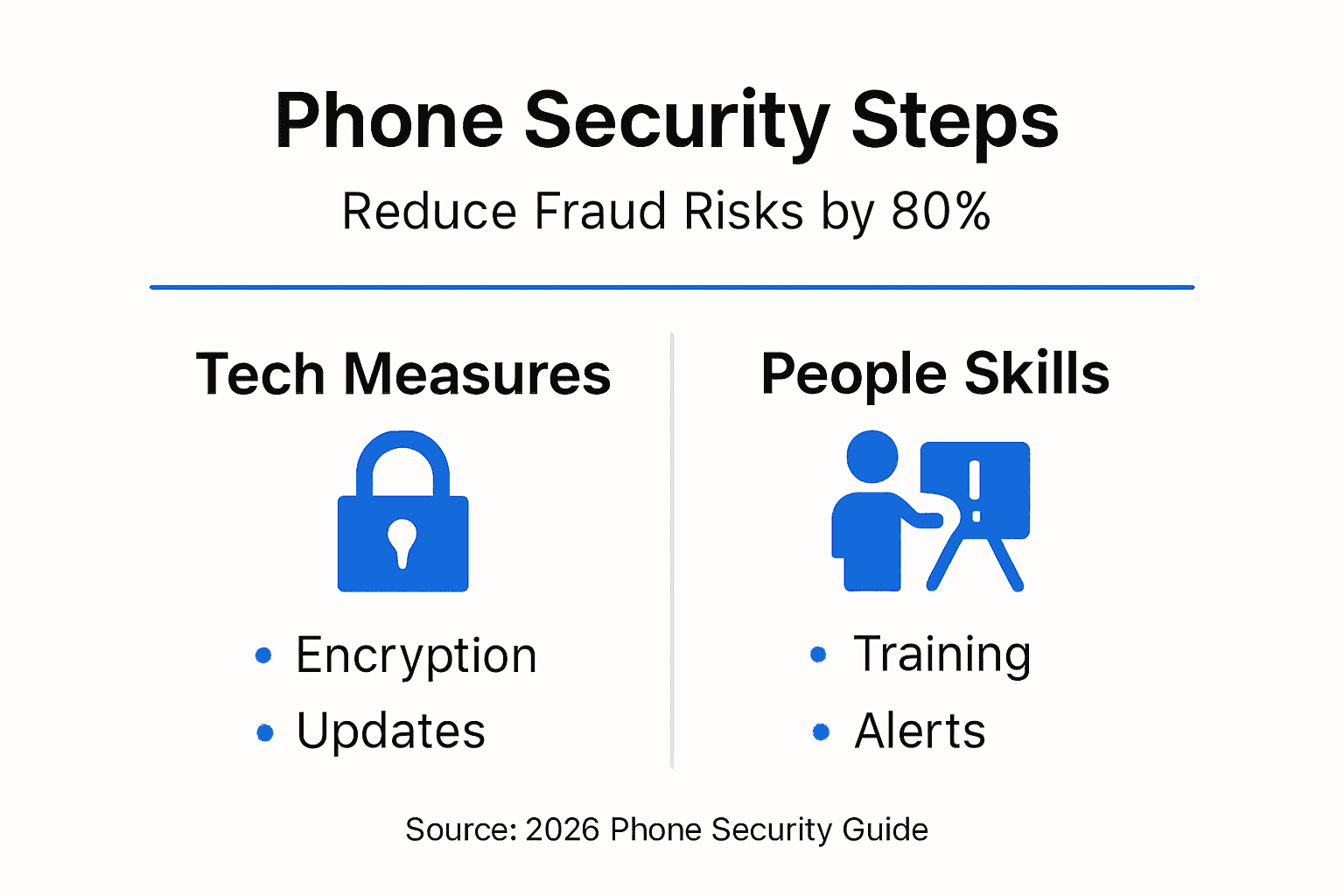
Small businesses lose an estimated $80 billion annually to phone system fraud and cyber attacks. Yet many SMB owners in Arizona and Colorado still trust outdated legacy systems, unknowingly increasing their exposure to sophisticated threats. This guide walks you through essential phone security basics and practical steps to protect your business communications, reduce fraud risks by up to 80%, and ensure compliance with federal regulations.
Table of Contents
- Introduction To Business Phone Security
- Common Threats To Business Phone Systems
- Regulatory Compliance Requirements For SMB Phone Security
- Technical Security Measures For Business Phones
- Common Misconceptions About Phone Security
- Employee Training And Security Awareness
- Managed Services For Phone Security
- Practical Steps For SMBs To Enhance Phone Security
- Secure Your Business Phone System With Voipcom Solutions
- Frequently Asked Questions About Business Phone Security
Key Takeaways
| Point | Details |
|---|---|
| Layered Security Required | Effective phone protection combines technical controls with employee training and policy enforcement. |
| Compliance Is Mandatory | HIPAA and FCC rules require specific security measures for businesses handling sensitive customer data. |
| VoIP Outperforms Legacy | Cloud phone systems provide stronger encryption and security than traditional PBX hardware. |
| Training Reduces Incidents | Educated employees prevent the majority of phone-based security breaches caused by human error. |
| Managed Services Save Money | Expert oversight delivers continuous monitoring, faster response, and predictable costs. |
Introduction to Business Phone Security
Your business phone system carries customer payment information, health records, proprietary data, and confidential conversations. Without proper security, you’re broadcasting this sensitive information to anyone listening. Legacy PBX systems are associated with 60% more security incidents than modern VoIP setups, yet many SMB owners continue using them based on outdated assumptions about reliability.
Understanding the landscape of phone security threats is your first defense. Common risks include:
- Call interception where attackers eavesdrop on conversations containing sensitive data
- Toll fraud that racks up thousands in unauthorized international calls overnight
- Service disruption attacks that take your phones offline during critical business hours
- Credential theft through phishing schemes targeting your phone system logins
Modern business phone system basics include built-in security features that legacy hardware simply cannot match. Cloud-based VoIP platforms encrypt your calls, require multi-factor authentication, and receive automatic security updates. The shift from copper wires to internet-based calling isn’t just about features; it’s about protection.
Recognizing phone phishing threats early prevents costly breaches. This guide equips you with actionable knowledge to secure your communications starting today, whether you’re planning a new business phone setup or hardening your existing system.
Common Threats to Business Phone Systems
Toll fraud represents the most immediate financial danger to SMBs. Attackers gain access to your phone system, then place hundreds of calls to premium-rate international numbers they control. You discover the breach when a bill for $15,000 arrives for calls made at 3 AM to obscure countries. These attacks happen fast, often completing in hours.
Vishing, or voice phishing, exploits human trust over phone lines. Criminals pose as IT support, vendors, or executives to extract passwords, financial information, or authorize fraudulent transactions. Unlike email phishing, voice calls feel more legitimate and urgent, making employees more likely to comply. Understanding phone scams and phishing tactics helps your team recognize manipulation attempts.
Eavesdropping risks expose everything discussed on unencrypted phone lines. Competitors, criminals, or unauthorized parties intercept calls containing:
- Patient health information and medical discussions
- Customer credit card numbers and payment details
- Strategic business plans and pricing negotiations
- Confidential employee performance or legal matters
Denial of service attacks flood your phone system with fake calls, preventing legitimate customers from reaching you. During peak business hours, this translates directly to lost revenue and damaged reputation. The threats targeting phone security continue evolving as criminals develop new techniques, making ongoing vigilance essential.
Pro Tip: Set up call volume alerts that notify you when unusual calling patterns occur, giving early warning of potential toll fraud before major charges accumulate.
Regulatory Compliance Requirements for SMB Phone Security
HIPAA and FCC regulations require businesses handling protected health information to enforce phone system security controls such as encryption and access logs. If your Arizona or Colorado business operates in healthcare, insurance, legal services, or financial sectors, compliance isn’t optional. Violations carry penalties ranging from $100 to $50,000 per incident, with potential criminal charges for willful neglect.
HIPAA mandates specific phone security measures:
- End-to-end encryption for all calls containing protected health information
- Access controls limiting who can retrieve voicemails or call recordings
- Audit logs tracking all system access and configuration changes
- Business associate agreements with your phone service provider
FCC regulations require telecommunications providers and businesses using phone systems for customer service to maintain reasonable security practices. This includes protecting customer proprietary network information, implementing authentication for system access, and maintaining incident response procedures. Even if you’re not directly regulated, customers increasingly expect these protections.
Compliance enhances trust and reduces exposure. When clients know their conversations are encrypted and access-controlled, they feel confident sharing sensitive information. VoIP security for healthcare SMBs addresses these requirements through built-in compliance features that legacy systems cannot match.
State-level regulations in Arizona and Colorado may impose additional requirements for data protection and breach notification. Consult with legal counsel to understand your specific obligations, then align your phone security accordingly.
Technical Security Measures for Business Phones
Use of encryption protocols like TLS and SRTP blocks 99% of interception-based attacks. Transport Layer Security (TLS) encrypts the signaling data that sets up calls, while Secure Real-time Transport Protocol (SRTP) encrypts the actual voice conversation. Together, they create an encrypted tunnel that prevents eavesdropping even if attackers access your network.
Multi-factor authentication (MFA) on administrative portals stops unauthorized access even when passwords are compromised. Instead of just entering a username and password, administrators must also verify identity through a mobile app code or text message. This simple addition blocks the vast majority of credential-based attacks.
Network segmentation isolates your phone system from other business systems. By placing phones on a separate virtual LAN (VLAN), you prevent attackers who breach your email server or file storage from accessing phone infrastructure. Firewalls between segments control which systems can communicate.
Regular updates close security vulnerabilities before criminals exploit them. Cloud-based systems receive automatic patches, while on-premise systems require manual updating. This difference explains why modern platforms maintain stronger security postures than legacy hardware.
| Security Feature | Legacy PBX | Cloud VoIP |
|---|---|---|
| Call Encryption | Optional, complex setup | Built-in, automatic |
| Multi-Factor Authentication | Rarely available | Standard feature |
| Security Updates | Manual, infrequent | Automatic, continuous |
| Access Logging | Limited capability | Comprehensive audit trails |
| Network Segmentation | Requires separate hardware | Software-defined, flexible |
| Compliance Tools | Additional cost | Included |
Implementing technical VoIP security measures doesn’t require massive IT expertise when you choose the right platform. Modern systems make encryption and authentication default settings rather than complex configurations. VoIP system optimization includes security hardening as a standard step.
Pro Tip: Enable session border controllers (SBCs) to filter malicious traffic before it reaches your phone system, adding an extra security layer that stops attacks at the network edge.
Common Misconceptions About Phone Security
Many SMB owners believe their legacy PBX system is more secure because it’s physically on-premise and isolated from the internet. The reality is opposite. These systems run outdated software with known vulnerabilities, lack encryption capabilities, and require physical access for updates that rarely happen. The false sense of security delays necessary upgrades.
Another dangerous myth suggests that phone breaches are rare and happen to other businesses. In truth, most attacks go unreported because companies fear reputation damage or don’t discover them until billing cycles reveal toll fraud. The actual exposure rate is significantly higher than public statistics suggest.
Passwords alone provide insufficient protection for modern threats. Attackers use automated tools to test thousands of password combinations per minute. Without MFA requiring a second verification factor, even complex passwords eventually fail. Yet many businesses still rely solely on password protection for administrative access.
Some owners assume their phone provider handles all security automatically. While reputable providers implement network-level protections, you remain responsible for:
- Configuring access controls and user permissions properly
- Training employees on security awareness and threat recognition
- Monitoring call patterns for suspicious activity
- Maintaining strong authentication practices
The belief that common phone security myths don’t apply to small businesses proves particularly harmful. Criminals specifically target SMBs because they typically have weaker defenses than enterprises but still process valuable data and transactions.
Pro Tip: Treat your phone system security with the same rigor as your financial accounts and customer databases, because attackers view them as equally valuable targets.
Employee Training and Security Awareness
Statistics show a majority of phone-based security incidents are caused by human error such as falling for phishing scams. Your technical defenses only work when employees understand and follow security protocols. A single person sharing system credentials over a vishing call can undermine your entire security investment.
Effective training teaches employees to recognize manipulation tactics. Attackers create urgency, impersonate authority figures, and request actions that bypass normal procedures. Training should include:
- Real examples of vishing attempts targeting similar businesses
- Verification procedures before sharing any sensitive information over the phone
- Proper handling of voicemails containing confidential data
- Reporting processes for suspicious calls or system behavior
- Password hygiene and why sharing credentials endangers everyone
Regular reinforcement matters more than one-time training. Brief monthly reminders through email, team meetings, or posted notices keep security awareness fresh. Make it conversational rather than punitive so employees feel comfortable reporting potential incidents.
Role-playing exercises help employees practice responding to social engineering attempts. Have managers periodically place test calls requesting password resets or sensitive information transfers. Employees who correctly refuse and report the attempt receive recognition, creating positive reinforcement.
Engaging employee phone security training reduces incident rates significantly. When your team becomes your first line of defense, attackers find fewer vulnerabilities to exploit.
Pro Tip: Create a simple verification phrase or callback procedure that employees use when anyone requests sensitive information by phone, turning potential breaches into routine security checks.
Managed Services for Phone Security
Managed services shift security monitoring and maintenance to experienced professionals who handle it continuously. Instead of reacting to breaches after they occur, managed providers watch for threats in real-time, block attacks automatically, and respond to incidents within minutes rather than hours or days.
Continuous monitoring detects anomalies that signal potential compromises. Unusual call volumes to international numbers, multiple failed login attempts, or configuration changes outside business hours trigger immediate alerts. Your managed service provider investigates and responds before minor issues become major losses.
Automatic updates keep your system protected against newly discovered vulnerabilities. Cloud platforms managed by experts receive security patches the moment they’re available. You never face the choice between maintaining operations and applying critical security updates.
| Service Model | Break-Fix Support | Managed IT Support |
|---|---|---|
| Security Monitoring | None, reactive only | 24/7 continuous |
| Update Management | Your responsibility | Provider handles |
| Incident Response Time | Hours to days | Minutes to hours |
| Cost Structure | Unpredictable, per-incident | Fixed monthly fee |
| Compliance Support | Additional services | Often included |
| Expertise Level | Varies by technician | Dedicated security team |
Local support availability in Arizona and Colorado means faster response when you need help. Your managed VoIP benefits include personalized service from teams who understand regional business needs and regulations.
Managed services deliver predictable costs that include security tools, monitoring, support, and updates in a single monthly fee. This predictability helps budget planning while eliminating surprise expenses from security incidents. The advantages of VoIP for SMBs multiply when professional management ensures your system stays secure and optimized.
Scalability becomes simple when your managed provider handles adding users, locations, or features without security gaps. VoIP benefits include flexible growth, and managed services ensure that expansion maintains security standards. Mobility with managed phone services lets remote workers stay connected securely.
Practical Steps for SMBs to Enhance Phone Security
Taking action starts with assessing your current situation. Follow these prioritized steps to strengthen your phone security affordably and effectively:
- Audit your existing system to identify vulnerabilities, compliance gaps, and outdated components requiring replacement or upgrade.
- Implement encryption protocols by enabling TLS for signaling and SRTP for voice traffic, ensuring all conversations are protected from interception.
- Enable multi-factor authentication on all administrative accounts and portals, blocking unauthorized access even when passwords are compromised.
- Provide security awareness training to all employees who use phones, focusing on recognizing vishing attempts and proper data handling.
- Review access permissions regularly, removing credentials for former employees and limiting administrative access to essential personnel only.
- Monitor call patterns for unusual activity like high-volume international calls or off-hours system access that may indicate compromise.
- Evaluate managed service providers offering local Arizona and Colorado support, comparing their security features, response times, and pricing.
- Calculate security ROI by comparing the cost of protection measures against potential losses from toll fraud, data breaches, and compliance violations.
Cost considerations should weigh prevention against recovery. A $5,000 toll fraud incident costs more than a year of managed security services. Data breaches carry additional costs including notification requirements, legal fees, and lost customer trust. Investing in phone security best practices proves far less expensive than recovering from preventable attacks.
Ensure your providers offer responsive local support. When security incidents occur, waiting hours for callbacks from distant support centers extends damage and downtime. Arizona and Colorado-based support teams understand regional business needs and provide faster, more personalized assistance.
Pro Tip: Start with quick wins like enabling MFA and conducting basic employee training, then build toward comprehensive managed services as budget and needs dictate, creating layered security progressively.
Secure Your Business Phone System with Voipcom Solutions
Protecting your business communications requires expertise, technology, and ongoing vigilance that challenges many SMBs. Voipcom delivers secure hosted PBX advantages through cloud-based systems with built-in encryption, automatic security updates, and comprehensive compliance tools.
Our managed VoIP advantages include continuous monitoring from security professionals, rapid incident response, and local support teams serving Arizona and Colorado businesses. We handle the technical complexity while you focus on running your business.
Choose scalable, compliant phone systems designed specifically for SMBs facing real security threats. Our transparent pricing eliminates surprise fees, while fully managed service covers setup, maintenance, training, and 24/7 support. Contact Voipcom to discuss how we can strengthen your phone security and reduce fraud risks today.
Frequently Asked Questions About Business Phone Security
How often should SMBs update their phone security protocols?
Review and update security settings quarterly at minimum, and immediately after any security incident or major software update. Regular audits catch configuration drift and ensure new employees receive proper access levels.
Can SMBs secure phone lines without switching to VoIP?
Some security measures like employee training and access controls apply to legacy systems, but fundamental protections like call encryption require modern VoIP platforms. Legacy hardware cannot match cloud-based security capabilities.
What signs indicate a phone system has been compromised?
Watch for unexplained international charges, degraded call quality, unexpected outbound calls in system logs, failed login alerts, or configuration changes you didn’t authorize. Any of these warrant immediate investigation.
Does regulatory compliance require hiring external consultants?
Not always. Many SMBs achieve compliance using provider tools, training resources, and built-in platform features. However, businesses in heavily regulated sectors often benefit from expert compliance audits and guidance.
Are there affordable phone security solutions for small budgets?
Yes. Managed VoIP services offer enterprise-grade security at SMB prices through economies of scale. The predictable monthly cost typically proves lower than potential losses from a single security incident, making protection affordable and cost-effective.